What is Email Threat Protection?
Email is a popular means of communication and is also the most effective tool used for committing cyber crimes.
The more knowledge cybercriminals gain about a targeted individual or business, the more successful they’ll be in executing an email-based attack. Strategic attacks on a business often involve using personal information, obtained through accessing social media sites and simple searches on search engines, to target an individual or small group. Cybercriminals know how to combine that information with social engineering and a spoofed address to provoke a response.

Email Is the Primary Threat Vehicle
Cybercriminals are ingenious and have years of experience developing email security threats. The vast majority rely on email as their primary threat vehicle. There are many categories of email threats. It’s essential to understand how they work so they can be deterred, identified, and eliminated.
- Visiting a malicious website
- Downloading music, applications, videos, or digital books
- Clicking on links for free games, demos, or to view an online seminar
- Opening an email attachment or clicking a link
- Data Wiper – A Data Wiper attack can delete files, operating system resources, and even reformat hard drives and solid-state drives. After an attack, a system may require a complete rebuild.
- Ransomware – Ransomware uses strong encryption to lock data and resources so they cannot be used. The system may boot but will not perform any tasks. The user must pay a fee to obtain the application and keys required to decrypt the system to return it to full operation. These attacks have been known to temporarily shut down many businesses and government institutions. The encryption is usually done using a cryptographic algorithm that is deemed unbreakable. Ransom payments are often made in crypto-currency, which is difficult to trace.
- Scareware – Scareware is malware designed to scare the user into taking unnecessary action. It uses social engineering to create a false perception that the user’s system is experiencing a severe problem or been exposed to a cyber-attack. The user must purchase unwanted software to remedy the problem.
- Spyware – Spyware is background malware that gathers information about a person or business. It targets specific data types such as web browsing history, keywords, credit card numbers, financial transactions, and login credentials. The information gathered is sent to another location where it will be used to commit further cybercrimes.
- Keylogger – Keyloggers are installed by clicking on a malicious attachment or link. The individual using the keyboard is unaware that their actions are being recorded and sent to another location.
- Fellow employees or business partners
- IT or human resource departments
- Services such as banks, insurance organizations, or credit card companies
- Healthcare or teaching institutions
- Entertainment venues, sports organizations, or clubs
- Lateral Phishing – Lateral phishing uses hijacked accounts to send phishing emails to one or many recipients. Since the email account is an actual account, the authenticity of the request is usually not questioned. It’s not unusual for a lateral phishing attack to involve all the members of an email address book. In some cases, phishing emails can be sent to an email group or even the entire company. They can also be designed as a chain email to spread beyond the initial lists. For example, a chain email can request people to donate money to a cause or click a malicious link to obtain a gift.
- URL Phishing – Clicking a URL to access a known entity, such as your bank, is second nature. Cybercriminals know that if they send a high volume of emails, a certain percentage of the recipients will select a recognized link without giving it a second thought. As an example, assume a cybercriminal obtains a list of email addresses from a specific bank. They create a login page that looks identical to the actual bank login plan. They notify the users that it is time to reset their passwords. If they send the email out to a thousand users, a percentage will provide their credentials.
- Spear Phishing – Spear phishing is focused on a single target. It’s sometimes referred to as ‘Whaling when targeting a high-level individual. It’s usually a person within an organization who has the authority to perform acts involving information, products, or money. The cybercriminal may pose as a high-level superior such as the president, CEO, or board member. They may request the individual to provide confidential customer information, ship products, or wire funds. They may also create a false sense of urgency and make the request on a Friday afternoon or before a long holiday break, thereby not providing the targeted individual with enough time to validate the request.
- Doe@USPPL.org
- Doe@USSPL.net
- JohnDoe@USPPL.co.inc
- Johnny@USSPL.com
Conversation Hijacking
Hijacking is an attack where the cybercriminal manages to infiltrate an email communication between employees, customers, suppliers, financial institutions, etc. They assume a role in the conversation or impersonate one of the previous participants. The other email participants have no reason to suspect that a member and communication have been compromised. This gives the cybercriminal the advantage needed to commit cybercrimes such a data theft or install malware.
Data Exfiltration
Data exfiltration is the unauthorized transfer of data from a system. It goes by many names, including data extrusion, exportation, data theft, data loss, and leakage. Deceptive and fraudulent emails can be used to obtain and export data to a location outside of the corporate firewall. By using email, the cybercriminal can obtain valuable information without needing to physically enter a facility.
Malware
Malware is malicious software designed to extort funds or disrupt business operations. Damage can be done to an application, operating system, network device, computer, server, client, or data storage system. Targets can be individuals, businesses, public organizations, or infrastructures such as transportation districts, power grids, or solar farms. Malware is dangerous in that it may be remediated but not eliminated. It may remain dormant and return at a later date to do further harm.
Malware can also hide in data backups. A business may eliminate malware but then reintroduce it by loading a data backup session still containing the malware. Malware can enter a business in many ways.
Malware can take many forms, such as computer viruses, worms, Trojan horses, ransomware, spyware, adware, rogue software, data wipers, and more.
Phishing
Phishing is a socially engineered psychological attack. Cybercriminals use different techniques to gain the trust of their target. This begins by using email to impersonate a person or entity known to the target. A phishing attack starts with an authentic-looking email source address and content. Common false email personas include,
Once the cybercriminal deceives the target into believing they are authentic, they progress to the next step, which is making a request. That may be on the same email or done over a series of emails. The goal is to have the target perform an act on the criminal’s behalf, such as divulge confidential information such as security and login credentials. There are different types of email phishing attacks.
Scamming
Email scamming uses various proven schemes to defraud targets of assets and information. As an example, the cybercriminal obtains the email addresses of people using a specific insurance company. They send out an official-looking email stating that there has been a lawsuit against the insurance provider. Customers who wish to receive compensation must click a link to a malicious website to register. Scamming emails use official email styles that a user would typically receive from an institution. The user would never suspect that the communication is not authentic.
Spoofing
Cybercriminals understand email protocols. They know how to create false accounts that appear very similar to authentic email addresses. Examples of email address variants would be,
Spammers and cybercriminals will use spoofed email addresses so that recipients trust the sender. Spoofing is also known as ‘Domain Impersonation’ and Service Impersonation.’
Spam
Email spam, or junk email, accounts for the majority of email traffic. They are unsolicited messages sent in mass to large groups of people. By definition, spam is bulk advertising mail in email form. Although spamming sounds like an innocent nuisance, it’s important to remember that most ransomware attacks start with spam emails. Despite many ways to filter out unwanted email, spam remains a significant challenge for organizations.
Hijacking is an attack where the cybercriminal manages to infiltrate an email communication between employees, customers, suppliers, financial institutions, etc. They assume a role in the conversation or impersonate one of the previous participants. The other email participants have no reason to suspect that a member and communication have been compromised. This gives the cybercriminal the advantage needed to commit cybercrimes such a data theft or install malware.
Data exfiltration is the unauthorized transfer of data from a system. It goes by many names, including data extrusion, exportation, data theft, data loss, and leakage. Deceptive and fraudulent emails can be used to obtain and export data to a location outside of the corporate firewall. By using email, the cybercriminal can obtain valuable information without needing to physically enter a facility.
Malware is malicious software designed to extort funds or disrupt business operations. Damage can be done to an application, operating system, network device, computer, server, client, or data storage system. Targets can be individuals, businesses, public organizations, or infrastructures such as transportation districts, power grids, or solar farms. Malware is dangerous in that it may be remediated but not eliminated. It may remain dormant and return at a later date to do further harm.
Malware can also hide in data backups. A business may eliminate malware but then reintroduce it by loading a data backup session still containing the malware. Malware can enter a business in many ways.
- Visiting a malicious website
- Downloading music, applications, videos, or digital books
- Clicking on links for free games, demos, or to view an online seminar
- Opening an email attachment or clicking a link
Malware can take many forms, such as computer viruses, worms, Trojan horses, ransomware, spyware, adware, rogue software, data wipers, and more.
- Data Wiper – A Data Wiper attack can delete files, operating system resources, and even reformat hard drives and solid-state drives. After an attack, a system may require a complete rebuild.
- Ransomware – Ransomware uses strong encryption to lock data and resources so they cannot be used. The system may boot but will not perform any tasks. The user must pay a fee to obtain the application and keys required to decrypt the system to return it to full operation. These attacks have been known to temporarily shut down many businesses and government institutions. The encryption is usually done using a cryptographic algorithm that is deemed unbreakable. Ransom payments are often made in crypto-currency, which is difficult to trace.
- Scareware – Scareware is malware designed to scare the user into taking unnecessary action. It uses social engineering to create a false perception that the user’s system is experiencing a severe problem or been exposed to a cyber-attack. The user must purchase unwanted software to remedy the problem.
- Spyware – Spyware is background malware that gathers information about a person or business. It targets specific data types such as web browsing history, keywords, credit card numbers, financial transactions, and login credentials. The information gathered is sent to another location where it will be used to commit further cybercrimes.
- Keylogger – Keyloggers are installed by clicking on a malicious attachment or link. The individual using the keyboard is unaware that their actions are being recorded and sent to another location.
Phishing is a socially engineered psychological attack. Cybercriminals use different techniques to gain the trust of their target. This begins by using email to impersonate a person or entity known to the target. A phishing attack starts with an authentic-looking email source address and content. Common false email personas include,
- Fellow employees or business partners
- IT or human resource departments
- Services such as banks, insurance organizations, or credit card companies
- Healthcare or teaching institutions
- Entertainment venues, sports organizations, or clubs
Once the cybercriminal deceives the target into believing they are authentic, they progress to the next step, which is making a request. That may be on the same email or done over a series of emails. The goal is to have the target perform an act on the criminal’s behalf, such as divulge confidential information such as security and login credentials. There are different types of email phishing attacks.
- Lateral Phishing – Lateral phishing uses hijacked accounts to send phishing emails to one or many recipients. Since the email account is an actual account, the authenticity of the request is usually not questioned. It’s not unusual for a lateral phishing attack to involve all the members of an email address book. In some cases, phishing emails can be sent to an email group or even the entire company. They can also be designed as a chain email to spread beyond the initial lists. For example, a chain email can request people to donate money to a cause or click a malicious link to obtain a gift.
- URL Phishing – Clicking a URL to access a known entity, such as your bank, is second nature. Cybercriminals know that if they send a high volume of emails, a certain percentage of the recipients will select a recognized link without giving it a second thought. As an example, assume a cybercriminal obtains a list of email addresses from a specific bank. They create a login page that looks identical to the actual bank login plan. They notify the users that it is time to reset their passwords. If they send the email out to a thousand users, a percentage will provide their credentials.
- Spear Phishing – Spear phishing is focused on a single target. It’s sometimes referred to as ‘Whaling when targeting a high-level individual. It’s usually a person within an organization who has the authority to perform acts involving information, products, or money. The cybercriminal may pose as a high-level superior such as the president, CEO, or board member. They may request the individual to provide confidential customer information, ship products, or wire funds. They may also create a false sense of urgency and make the request on a Friday afternoon or before a long holiday break, thereby not providing the targeted individual with enough time to validate the request.
Email scamming uses various proven schemes to defraud targets of assets and information. As an example, the cybercriminal obtains the email addresses of people using a specific insurance company. They send out an official-looking email stating that there has been a lawsuit against the insurance provider. Customers who wish to receive compensation must click a link to a malicious website to register. Scamming emails use official email styles that a user would typically receive from an institution. The user would never suspect that the communication is not authentic.
Cybercriminals understand email protocols. They know how to create false accounts that appear very similar to authentic email addresses. Examples of email address variants would be,
- Doe@USPPL.org
- Doe@USSPL.net
- JohnDoe@USPPL.co.inc
- Johnny@USSPL.com
Spammers and cybercriminals will use spoofed email addresses so that recipients trust the sender. Spoofing is also known as ‘Domain Impersonation’ and Service Impersonation.’
Email spam, or junk email, accounts for the majority of email traffic. They are unsolicited messages sent in mass to large groups of people. By definition, spam is bulk advertising mail in email form. Although spamming sounds like an innocent nuisance, it’s important to remember that most ransomware attacks start with spam emails. Despite many ways to filter out unwanted email, spam remains a significant challenge for organizations.
Download our latest eBook. This new approach to networking comprises a set of truly integrated, cloud-managed security services delivered on-prem or in the cloud with centrally managed security. Learn how to:
- Reduce complexity and operational overhead
- Deliver ease of use/transparency for users
- Enhance security with zero-trust network access

URL filtering and Brand Protection
- DKIM – Domain Keys Identified Mail is a method used to detect false sender addresses often associated with phishing and spam. DKIM also checks that an email from a specific domain is authorized by the owner of that domain.
- SPF – Sender Policy Framework is an email authentication method that specifies the mail servers authorized to send emails for the organization’s domain. It is used to prevent spammers from illegally sending messages on behalf of a business.
- DMARC – Domain-based Message Authentication, Reporting & Conformance is an email authentication protocol. It gives email domain owners the ability to protect their domain from unauthorized use.

Email Advanced Threat Protection
To ensure email advanced threat protection, additional layers should be added.
Deep Inspection
Email threat protection services must include deep message and attachment analysis with spam, malware, and phishing filtering. Outgoing emails should be inspected to guard against data theft. The system should also protect against ‘backscatter’ and ‘mail bombs’ to prevent the overflow of user mailboxes.
Compliance
An email threat protection service should support legal and regulatory compliance. Authorized emails destined for a client may be sensitive and contain confidential information. The email service should be configured with policies, including integration with digital rights management, that identifies such data. It will either encrypt the entire data set or use tokenization to scramble the sensitive portion of the communication.
Isolation
Global email policies should block or send any suspicious messages to a quarantine zone or sandbox outside the organization’s infrastructure until the emails can be investigated.
Control
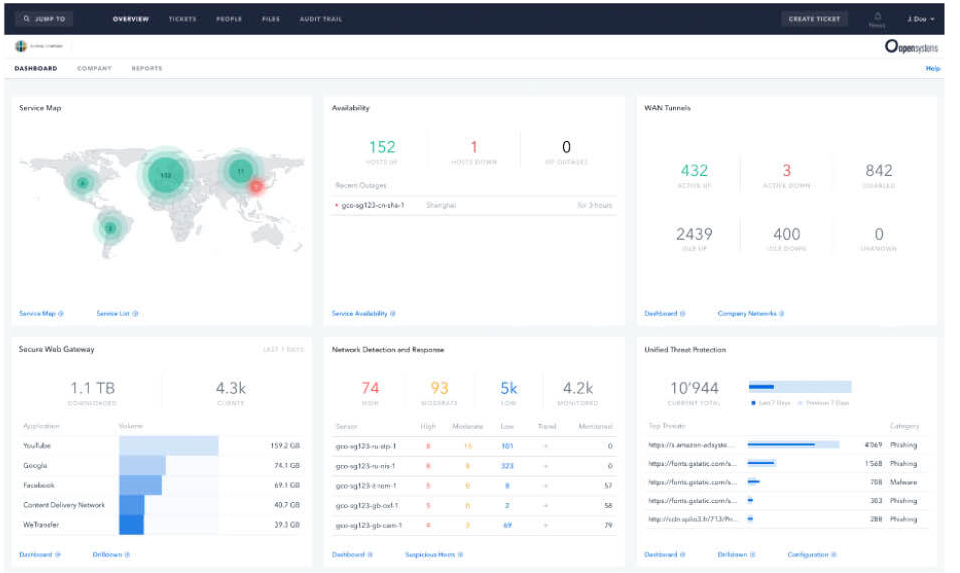
Management, monitoring, and reporting must be fully integrated into the secure email service. It’s essential to provide real-time mail traffic metrics down to the individual message for both incoming and outgoing emails. Current and historical details on incoming and outgoing queues, threat types, network usage, and system loads should be included. System security management should include access to all email and system-specific configuration settings and policy rules.
Email threat protection services must include deep message and attachment analysis with spam, malware, and phishing filtering. Outgoing emails should be inspected to guard against data theft. The system should also protect against ‘backscatter’ and ‘mail bombs’ to prevent the overflow of user mailboxes.
An email threat protection service should support legal and regulatory compliance. Authorized emails destined for a client may be sensitive and contain confidential information. The email service should be configured with policies, including integration with digital rights management, that identifies such data. It will either encrypt the entire data set or use tokenization to scramble the sensitive portion of the communication.
Global email policies should block or send any suspicious messages to a quarantine zone or sandbox outside the organization’s infrastructure until the emails can be investigated.
Management, monitoring, and reporting must be fully integrated into the secure email service. It’s essential to provide real-time mail traffic metrics down to the individual message for both incoming and outgoing emails. Current and historical details on incoming and outgoing queues, threat types, network usage, and system loads should be included. System security management should include access to all email and system-specific configuration settings and policy rules.
Protecting users and corporate networks from email-based cyber-threats isn’t a simple one-technology answer. It involves a variety of devices and services to create a multi-layered approach. Secure internet gateways, secure email gateways, CABSs, firewalls, and EDR all provide levels of security services that prevent threats.
Contact our customer advocates and learn about advanced email protection services. Discover more about implementing a complete cybersecurity posture with MDR (Managed Detection and Response) or SASE (Secure Access Service Edge).


Leave Complexity
Behind
To learn how Open Systems SASE Experience can benefit your organization, talk to a specialist today.
Contact Us