
Insurance
Securely Accelerate Your Insurance Operations
Insurance organizations with operations spread across regions or continents rely on secure worldwide IT networks that can deliver efficient, continuous access while protecting systems, end users and the brand itself.

Meet All Your IT Challenges
Maintain an Ultra-Reliable Network
Ensure high availability and 24x7 expert-level support
Complement SD-WAN with DevOps
Protect your most valuable assets from cyberattacks
Enable Global, Policy-based Compliance
Deliver complete, audit-ready enforcement processes
Extend Protections to Mobile Users
Provide secure remote access via user profiles
Ensure Network Reliability
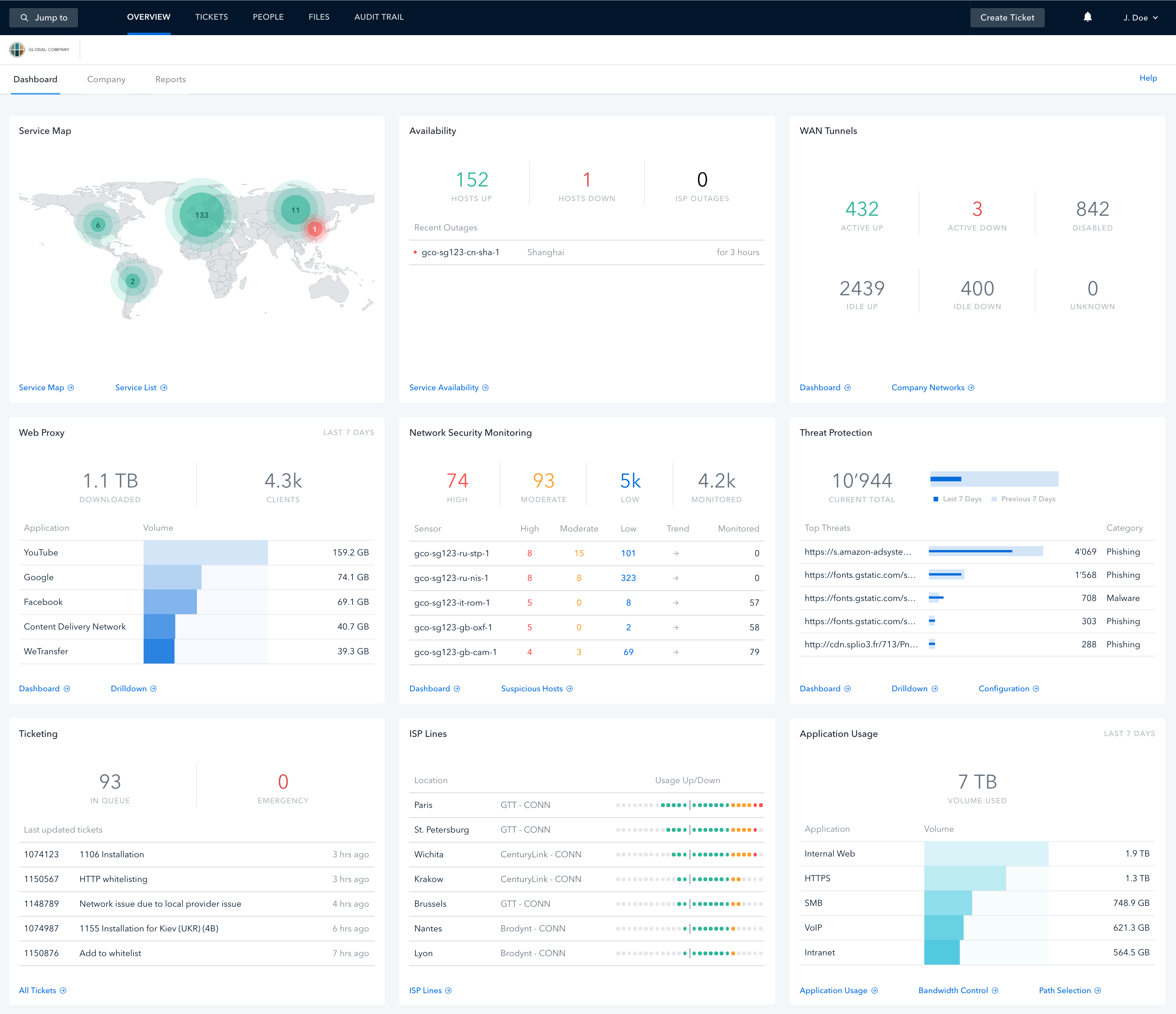
All your efficiency enhancement initiatives – like robotic process automation (RPA) – don’t mean much without a highly available network on which to operate. Open Systems incorporates quality, flexibility, and reliability at every level – hardware, lines, and third-party connectivity providers – so that your uptime gets maximum protection. Better still, we deliver an expert-level, 24×7 Network Operations Center (NOC) to proactively monitor and remediate issues before they impact your business.

Elevate Policy-based Security Processes
Complement and extend your existing enforcement processes while offering a transparent audit trail at every stage. Open Systems provides effortless integration with your existing compliance architecture without creating new overhead. Our Secure SD-WAN uniquely enables organizations to apply their desired policies globally and granularly across the network—while at the same time our NOC engineers seamlessly adapt to customers’ ticketing workflows.
Extend Secure Protections to Your Mobile Workforce
Maintain a consistent security posture – and fast, reliable network access – regardless of user location. Our ZTNA as well as Mobile Entry Point (MEP) technologies provide every user a secure connection that we tailor to the user’s particular access profile: firewall, web, and email protections are automatically applied for all clients according to their credentials. Create a globally distributed, fine-grained threat detection network through our edge-deployed Network Detection & Response (NDR)

Leave Complexity
Behind
To learn how Open Systems SASE Experience can benefit your organization, talk to a specialist today.
Contact Us

