LAN Firewall
Simplify and Enhance LAN Security
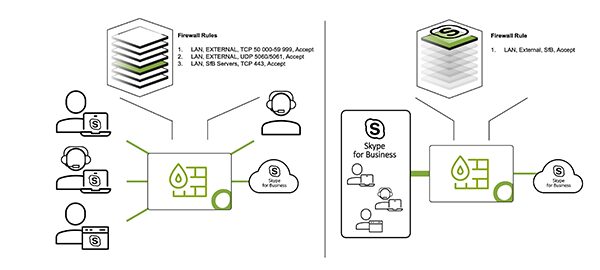
When reaching a certain size, HQs and branch locations suddenly have to cover lots of different endpoints like guest wifi, printers & scanners, R&D, IoT, … meaning more local access use cases like internal user who wants to print a document, guest wifi needing access to Internet, …
Handling that kind of traffic on the SD-WAN firewall can lead to performance bottlenecks. Also usually the local policy is rather loose, leading to security gaps. If itsn’t, then it means the policy is complex, having to deal with not only the local use cases, but all of the Internet and WAN use cases as well.
That’s why it is essential to dedicate a LAN firewall to this task and perform LAN segmentation

How We Protect Your Network
Dedicated FW
While theoretically feasible on a single appliance, SD-WAN and LAN traffic should be split when the complexity arise.
This way the policy are simpler to maintain and the performance bottleneck is removed.
LAN Segmentation
In order to mitigate lateral movement in case of a breach, a thorough network segmentation should be implemented on the LAN firewall.
Open Systems provides technical support to organizations to successfully implement LAN segmentation, therefore increasing their security posture.
While theoretically feasible on a single appliance, SD-WAN and LAN traffic should be split when the complexity arise.
This way the policy are simpler to maintain and the performance bottleneck is removed.

In order to mitigate lateral movement in case of a breach, a thorough network segmentation should be implemented on the LAN firewall.
Open Systems provides technical support to organizations to successfully implement LAN segmentation, therefore increasing their security posture.
Leave Complexity
Behind
To learn how Open Systems SASE Experience can benefit your organization, talk to a specialist today.
Contact Us