
A new reality for energy leaders
Energy is one of the most targeted sectors for cyberattacks, and leadership is increasingly accountable for technology risks that were once treated as IT issues.
-> Discuss with Steve Mathis how other leaders are addressing OT risk
How the operating reality of energy networks has changed
The energy sector has evolved faster than the security assumptions it was built on. What were once clearly separated environments — business systems and operational technology — now rely on shared infrastructure, shared access, and shared vulnerabilities.
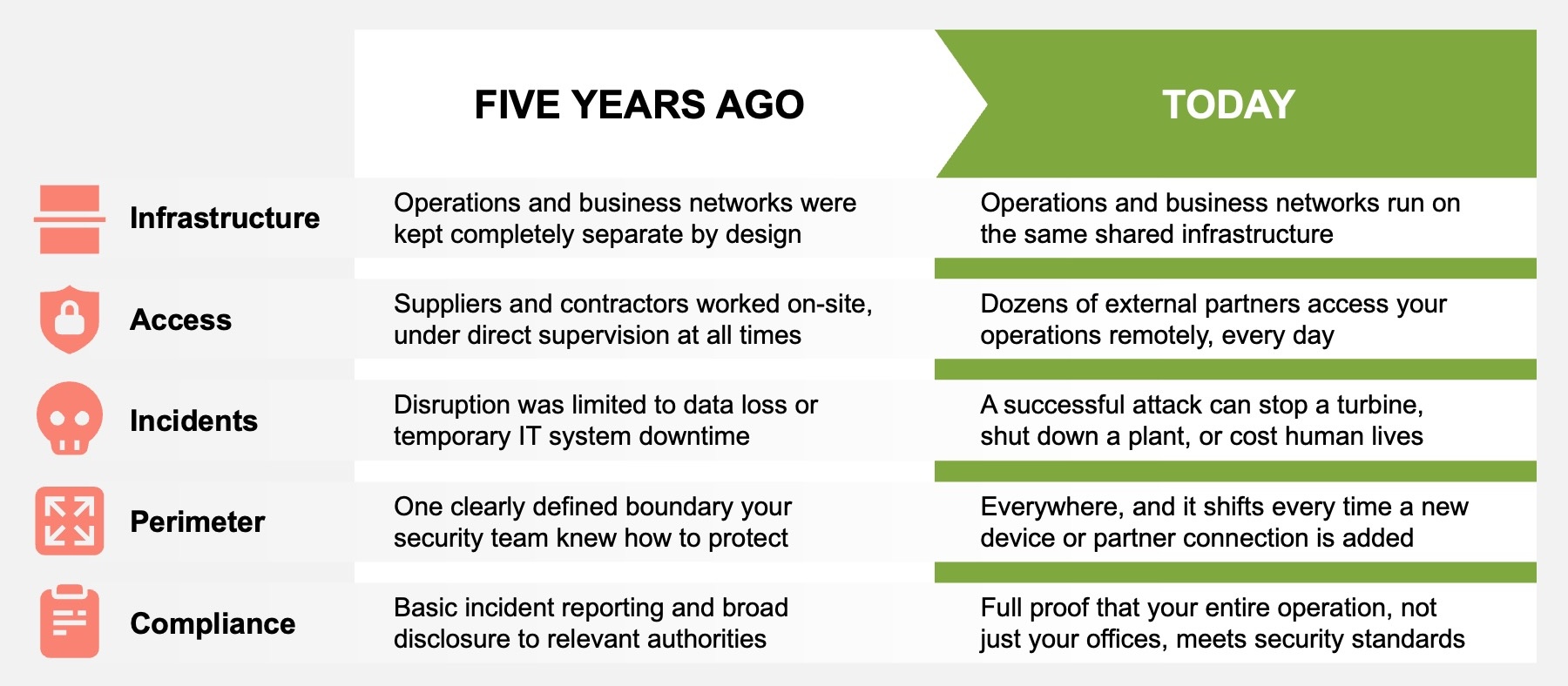
This shift not only changes how energy operations run, but also what is at stake when something goes wrong.
-> Read here how IT/OT convergence has fundamentally changed operational security
What this means for energy leaders
In connected environments, IT decisions directly shape outcomes that senior leaders are accountable for, with immediate, tangible consequences across the entire organization.
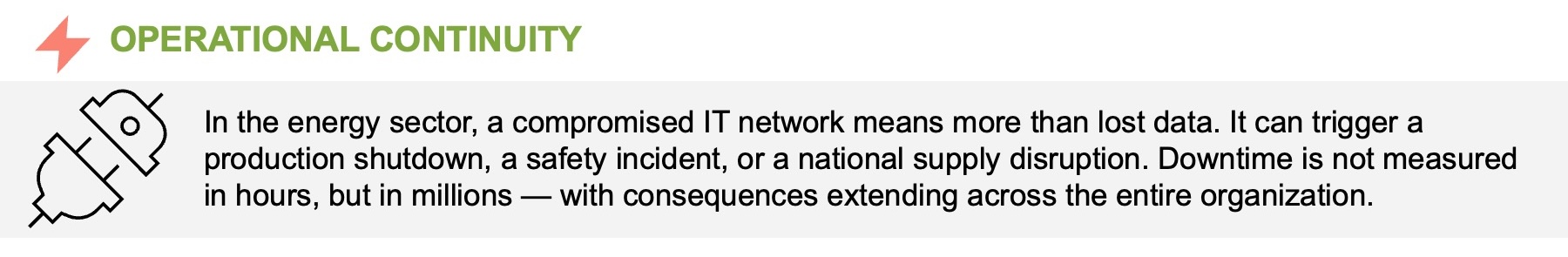
Understanding these risk areas is the first step toward managing them and deciding where leadership attention and ownership are required.
-> Read our practical Guide: Protecting Industrial Operations in the Era of IT/OT Convergence
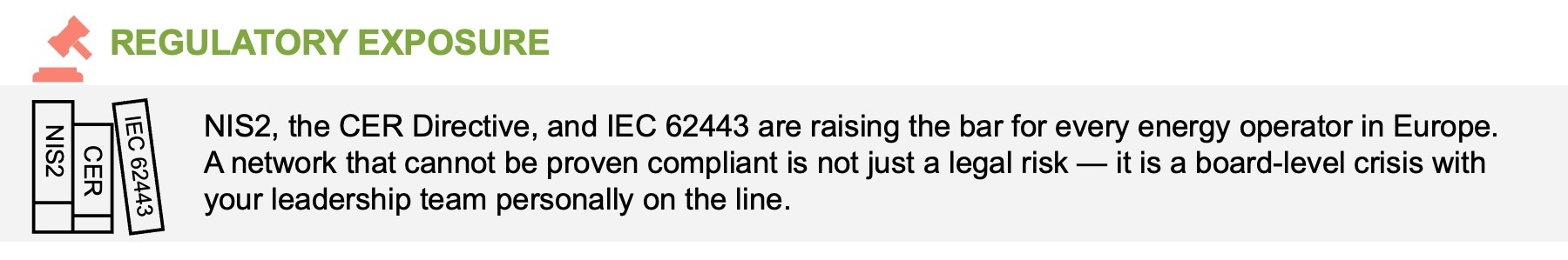
The regulatory pressure is real, and it’s personal
Senior leaders within critical infrastructure — technical or not — are increasingly expected, not only to approve and oversee cyber risk measures, but also to understand the risks and their operational impact.
Fragmented vendor setups, often the result of siloed decisions, make meaningful oversight difficult. To meet regulatory expectations, energy leaders must be deliberate in provider choices, ensuring IT decisions reflect operational realities.
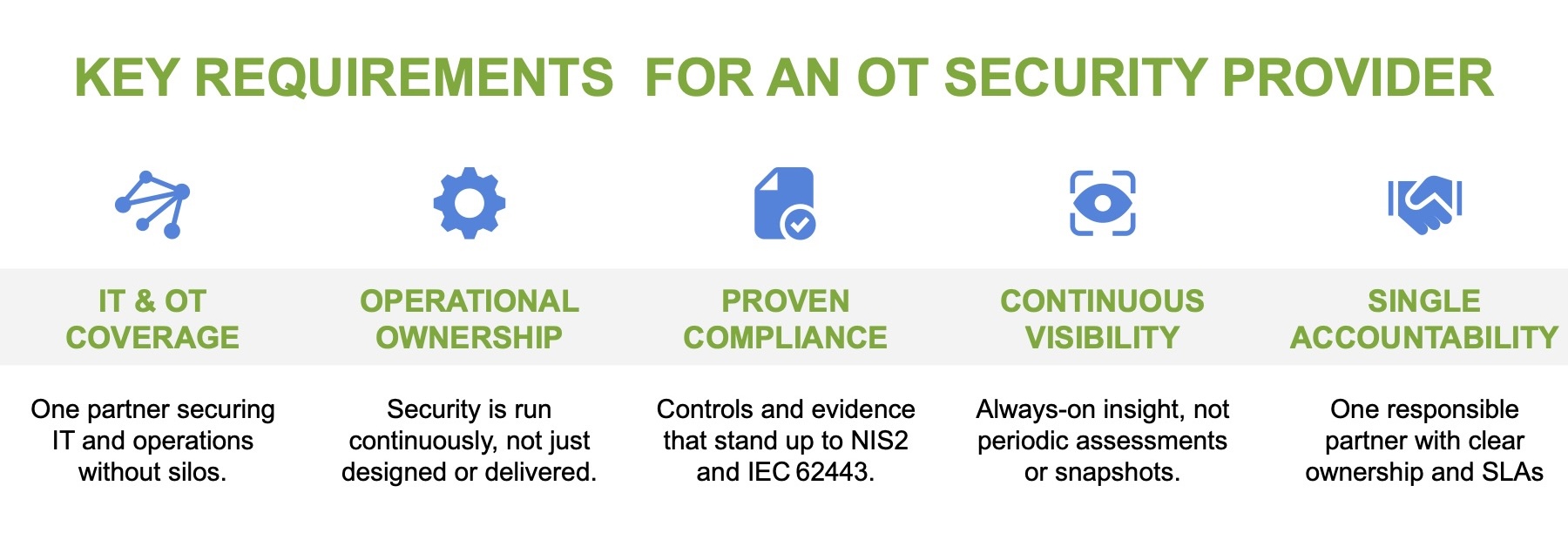
Your provider can either make or break your ability to comply with critical-sector regulations. Choose wisely, and regulatory compliance can become a strategic advantage rather than an ongoing burden.
-> Learn what effective OT security partners do differently
Turning complexity into something manageable
Managing security and compliance in complex IT and operational environments is rarely about tools. At Open Systems, we provide sustained operational support built on three fundamentals:
- Experience securing legacy and operational systems where long‑lived technologies now interact with modern IT.
- Hands‑on support for regulatory requirements, including NIS2 compliance and IEC 62443‑aligned operations.
- An operating model built for continuous control, clear accountability, and regulatory evidence over time.
In practical terms, we support organizations at every stage of the OT security journey.

How does this play out in your operating reality? Exchange perspectives on technology risk, regulatory pressure, and operational realities with Steve Mathis, Chief Customer Officer and OT security expert.
-> Book a no-commitment consultation with Steve Mathis, Chief Customer Officer at Open Systems
Leave Complexity
Behind
To learn how Open Systems SASE Experience can benefit your organization, talk to a specialist today.
Contact Us

